CrowdStrike Deep Dive
On July 19th, more than eight million computers around the world crashed, with the cause of the crash coming from an unknown source: CrowdStrike. Let's explore the story behind this company.
Welcome to the 90th Pari Passu Newsletter.
Today we are exploring a company whose popularity has recently increased for the wrong reasons. On July 19th, more than eight million computers around the world crashed, with the cause of the crash coming from an unknown source: CrowdStrike.
In this edition of Pari Passu, we’ll delve into the cybersecurity landscape, and how CrowdStrike has differentiated itself from key competitors. As a first mover in the sector, Crowdstrike saw triple-digit growth for more than a decade and fostered one of the most loyal customer bases in software.
Yet how did such an under-the-radar company face such a disastrous crash?
Let’s explore the story of Crowdstrike, what led to the recent outage of the Windows operating system, and how the company can take steps to avoid a future system failure.
But first, a message from 10 East
10 East, led by Michael Leffell, allows qualified individuals to invest alongside private market veterans in vetted deals across private credit, real estate, niche venture/private equity, and other one-off investments that aren’t typically available through traditional channels.
Benefits of 10 East membership include:
Flexibility – members have full discretion over whether to invest on an offering-by-offering basis.
Alignment – principals commit material personal capital to every offering.
Institutional resources – a dedicated investment team that sources, monitors, and diligences each offering.
10 East is where founders, executives, and portfolio managers from industry-leading firms diversify their personal portfolios.
There are no upfront costs or minimum commitments associated with joining 10 East.
Section 1: History
The First Anti-Virus Solutions
The first cybersecurity antivirus solution was launched by the company McAfee in 1987, followed by an antivirus solution that was launched by Symantec in 1991 [1].
McAfee: is the oldest global cybersecurity company that works in all areas of computer security, and was eventually acquired by Intel in 2010 for $7.7bn.
Symantec: is a provider that started at the same time as McAfee and is known for their “Norton antivirus software”. Symantec was acquired in 2019 by Broadcom for $10.7bn.
Anti-virus technology is a set of software solutions that aim to prevent malware from encroaching on an endpoint in a computer system [1].
Malware: a set of malicious software in a system that enables access to sensitive information for sabotage; examples of malware include attachments, phishing emails, or malicious software that users may download, incurring dangerous software.
Endpoints: the key input points in a software system. These endpoints consist of all types of systems from servers and desktops to mobile devices.
However, these early solutions were too slow to protect against evolving malware attacks. Specifically, the introduction of ransomware attacks in the late 2000s created an increased financial incentive for malware attackers. Ransomware is the process of using malware to access sensitive information and then hold it for ransom. Hackers could execute these attacks quickly and at a large scale which led to a 43% increase in ransomware attacks between Q4 2020 and Q1 2021 [1].
Additionally, there were several other pain points in legacy cybersecurity software that created space for disruption.
First, these legacy systems could only protect a system against malware attacks that had been previously identified as malicious [1].
This became a significant issue, as more and more new malware attacks proliferated, overwhelming the prevention capabilities of legacy cybersecurity systems.
By 2007, 5.5mm new malware samples were identified, and by 2013 there were an estimated 400 thousand new malware samples being reported each day.
Second, many firewalls used by the legacy systems incorporate trust but verify technology to allow users to access their sensitive information. The issue with this system is that malware attacks only had to circumvent a system once to access sensitive data, as the system would verify them as a trusted actor for their future system entrances [1].
Firewall: A firewall is a security system that controls the network traffic entering a secure system based on predetermined security rules.
Trust but verify: refers to a one time verification requirement to enter the sensitive system within a software platform.
Third, legacy systems use cybersecurity software that tries to stop malware throughout the system, or before it actually enters a platform that holds sensitive data [2].
While in theory this strategy provides wider observability for clients, it also means that it often expands resources to monitor the stretch of the security system.
Oftentimes, while monitoring the whole system, these wide observability solutions would miss minute malware software that could extract sensitive data unprotected.
It was clear that this wide-stretched approach to cybersecurity was inefficient, and clients started looking for centralized software security platforms with more detailed monitoring.
It became evident to many customers that they required a cybersecurity system that adapted to security requirements, rather than providing one-time malware prevention platforms.
Enter: Crowdstrike
Crowdstrike’s founder, George Kurtz, noticed many initial problems when he was the Chief Technology Officer (CTO) and McAfee. Kurtz first joined McAfee after he sold his own cybersecurity startup to the company in 2004 [1][2].
At McAfee, Kurtz was deeply unhappy with the firm’s security system, citing its many inefficiencies and lack of protective capabilities. After many offers to become a general manager, he finally accepted a higher position to work as CTO of the company.
It was at the CTO position that Kurtz gained insight into the specific problems that many customers faced in cybersecurity. One notable story is when Kurtz was on a flight and he saw a customer that struggled to download McAfee software for over 20 minutes.
This gave Kurtz the initiative to start a more efficient cybersecurity business; one that provided better solutions for clients with a greater ease of access.
On August 29, 2011, George Kurtz created a twenty five page slide deck that he presented to Warburg Pincus on a company that provided endpoint detection and response (EDR) with advanced AI technology. The pitch was a success, and Kurtz ended up receiving $25mm in seed funding, one the highest seed funding rounds in the software industry [1][2].
Endpoint Detection & Response (EDR): This type of cybersecurity focuses on monitoring endpoint traffic, like iPhone texts, PC emails, or sensor signals, to detect malware, rather than scanning the entire network. By centralizing detection at endpoints, companies can more accurately identify potential threats entering their systems..
Warburg Pincus: is a technology-oriented private investment firm that mostly invests in growth stage or late stage technology companies. Crowdstrike was one of their unique investments as the company was at a very early stage when they received funding. However, Warburg’s past relationship with the founder provided them with conviction on the investment.
Instead of having to expend resources to actively find the malware, Kurtz theorized Crowdstrike could increase its efficiency by focusing on security at key endpoints. The malware could now be caught in specific portions of the system, rather than having to search for it throughout the platform.
Two of Kurtz’s close friends at McAfee, Dmitri Alperovotch and Gregg Marston, joined Crowdstrike as the CTO and CFO. Alperovotch was previously the VP of Threat Research at McAfee making him a strong candidate to strengthen the technology at Crowdstrike, and Marston financial expertise made him a notable choice for CFO.
Crowdstrike’s Transition to Software (2011-2013)
Starting in 2011, Crowdstrike’s first product was more services oriented, with Kurtz and his team manually working with clients to detect and respond to cyber attacks. As the firm worked with more and more clients on various projects, they slowly expanded their intelligence in the cybersecurity space and reached a head count of several hundred employees [2].
This period had a rise in concentrated cyber attacks, making Crowdstrike’s services even more sought after [2].
These attacks were mainly from Advanced Persistent Threat (APT) groups, known for their prolonged and undetected attacks, that are usually geared toward stealing data rather than damaging the software system.
In response, many companies realized the significance of trust building in cybersecurity. They were more transparent about the threats to other companies, and worked collectively with cybersecurity providers for stronger prevention.
This led to an exponential growth in cybersecurity education among industry clients, and presented a catalyst for CrowdStrike to expand.
Between 2011 and 2013, software engineers at Crowdstrike took advantage of this growth in demand, and started to experiment with a cloud-based software cybersecurity system [2].
The "cloud" is a platform delivering computing services (storage, processing, networking, etc.) over the internet, allowing clients to rent compute resources without physical servers. This flexibility enabled Crowdstrike to expand its cybersecurity capabilities beyond physical data center limitations.
The prototype software was first released in blogs by the software developers at CrowdStrike, as they hoped to gain insight rather than sell the product. To their surprise, many companies found these blogs and pre-ordered the software product before it was launched, giving Kurtz conviction in his software and bolstering the development process.
A key feature of CrowdStrike’s go-to-market strategy (GTM) was its incident response services that quickly generated sales leads for the company. Incident response is a service that combs over a software platform after it has been breached, “post-mortem”, to recreate the incident and find its causes. Kurtz famously refers to incident response as the “Ghostbusters” of cybersecurity. Crowdstrike’s incident response services allowed them to gain intelligence on malware threats that they used to further enhance their cybersecurity software solutions.
The Introduction of Falcon
In June 2013, CrowdStrike launched its antivirus package “Falcon”, symbolizing the speed and precision that the firm aims to deal with cybersecurity threats. The excitement from the new product quickly excited investors, leading Crowdstrike to raise $30mm at a $140mm valuation in a Series B investment led by Accel Partners [3][4].
The funding was primarily used for the company’s GTM initiative, by educating clients about the company’s security solutions and then integrating CrowdStrike’s EDR products into each customer’s platform. With this initial spend, CrowdStrike quickly took part in many notable cyberattack prevention cases and built a name for itself.
In March 2014, CrowdStrike assisted the US Department of Justice in charging five Chinese hackers from "PLA Unit 61486" with cyber espionage. The hackers sent malware to business executives, enabling remote access to their computers and extraction of sensitive information [5].
In May 2015, CrowdStrike released information about "VENOM," a critical vulnerability affecting many big data providers. This pro-bono service, done without client incentive, demonstrated their commitment to security over monetary gain [7].
In June 2016, after being hired by the Democratic National Committee, CrowdStrike found evidence of Russian tampering in the US election. With federal clients, CrowdStrike has expanded its services beyond traditional business-to-business (B2B) cybersecurity to serve a wider range of clientele [8]. Since then, the number of customers has compounded steadily

Fun fact, CrowdStrike uses code names for each cyberattack group to maintain anonymity. Chinese espionage groups are labeled with "Panda," while Russian groups end with "Bear," reflecting their cultural origins. While these labels add a light-hearted element to the company, they’re also essential to CrowdStrike's intelligence operations [2].
Fundraising & Expansion
The increased demand for CrowdStrike, along with its capabilities to serve each client, allowed Crowdstrike to raise $455mm between 2015 and 2018.
In contrast with the previous rounds, these capital raises were mostly used for product development to further differentiate Crowdstrike from its competitors. Between 2016 and 2018, Crowdstrike launched Falcon Prevent, Discover, and Complete which greatly contributed to the company’s client expansion. An overview of each product is provided below in the “Company Overview” section.
Finally, with Crowdstrike’s influx of organic growth in new customers, and up-selling existing clients with higher quality products, the company eventually pursued an IPO on June 12, 2019 [10]. See below its market cap since the IPO.

Section 3: Company Overview
Company Overview
As we all know by now, CrowdStrike is a provider of software cybersecurity solutions to enterprise clients. The company focuses on endpoint detection and response, AI-enabled malware detection, cloud-based monitoring and malware intelligence. Currently Crowdstrike has almost nine thousand employees, and has international offices that serve clients around the globe [11].
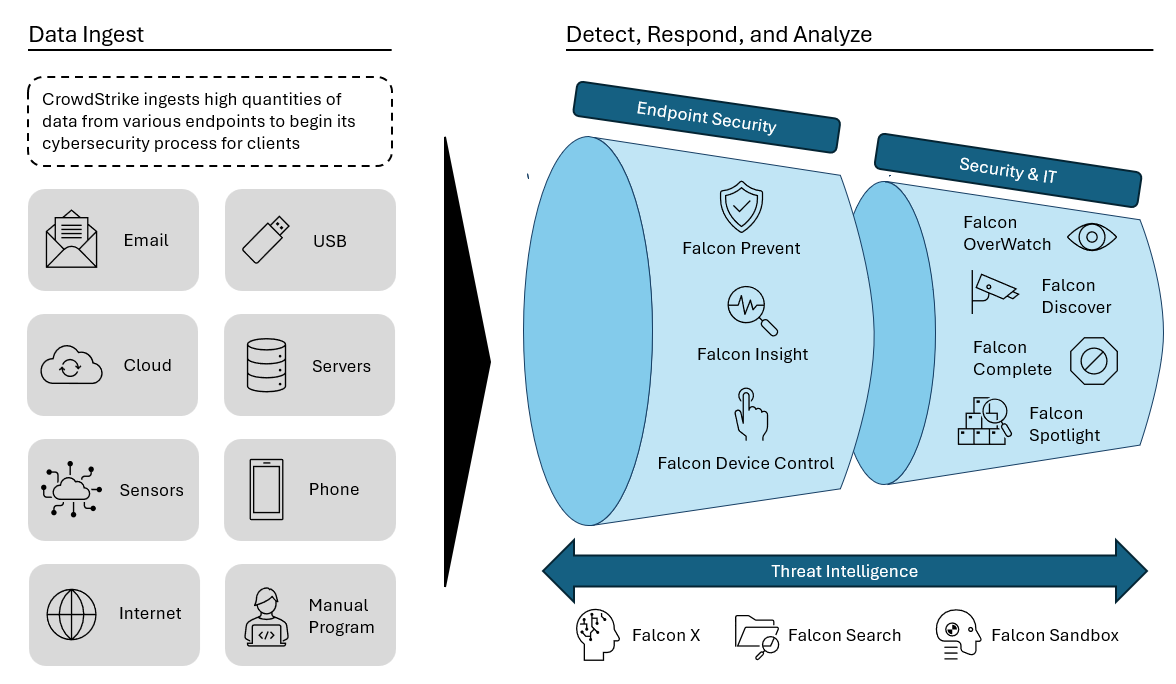
CrowdStrike’s Falcon products perform four key functions: ingesting client data, detecting malware, responding to attacks, and analyzing past threats to predict future ones. Clients can select from subscription packages with varying Falcon products, typically charged per endpoint monthly.
Ingestion: is the process of taking various types of data from endpoints and processing it for malware. For example, CrowdStrike may ingest the email data of a client so that it can be further analyzed for malware risk. All of CrowdStrike’s products have ingestion capabilities, as it forms the first step to the cybersecurity process.
Processing/Detection: The data analysis to find malware is usually referred to as “Endpoint Security” by CrowdStrike, as most of the data is being analyzed from digital endpoints such as USBs, iPhones or computers. CrowdStrike has three products in this category: Falcon Prevent, Insight, and Discover.
Response: CrowdStrike’s Security & IT division handles response to malware attacks. These are typically done through automated responses, as well as manual human responses to cyberattacks as a second layer of defense. The products in this category are Falcon OverWatch, Discover, Complete, and Spotlight.
Predictive Analysis: through CrowdStrike’s Threat Intelligence products analyze past malware data to prevent future threats. This continuous analysis occurs during and after detection and response, always running to predict new threats. This category, available only in the premium package, includes Falcon X, Search, and Sandbox..
Additionally, a graphic that portrays how the Falcon products work together is provided below.
Core Technology
As discussed above CrowdStrike’s cybersecurity technology “Falcon” operates through endpoint detection and response (EDR). Falcon is virtually attached to each of a client’s endpoints in the cloud, and automatically receives information about different events in the network. An event refers to any action that occurs within the cloud environment, such as a file being opened, a system being deleted, or a document being renamed [19].
CrowdStrike’s event recognition occurs across different layers of the cloud: virtual machines, nodes, and containers. Containers are like individual environments running their own programs. Nodes connect these containers, while the virtual machine directs tasks between the containers [19].
Virtual Machines: or “kernel code” is the operating layer of a software system, offering broad analysis and control but with less detail.
Node: connect containers in a system. Falcon's deployment here detects threats after they’ve passed through a container, providing detailed threat detection but less control compared to the virtual machine layer.
Container: are the smallest system components, often managed by software systems such as Kubernetes or Docker. Falcon focuses on relaying information from each of these containers, and potentially terminating them if the malware is too dangerous.
Thus, Falcon's deployment in containers offers granular analysis but requires high processing power, while deployment in virtual machines provides broader control with less detail
Once events are received through the virtual machine, node, or container, they are sent to CrowdStrike’s Threat Graph. The Threat Graph analyzes events across multiple dimensions, such as time, behavior, and network activity, unlike traditional cybersecurity platforms that operate in two dimensions, like the rows and columns in Excel. By analyzing events across multiple dimensions, CrowdStrike and its clients can more accurately determine if an event poses a potential threat [19].
Finally, after the data has been displayed on a the Threat Graph, CrowdStrike uses rule-based decision making and AI to analyze if an event is a malware threat.
Rule-Based Decision Making: Traditionally used by cybersecurity firms, this approach involves human analysts creating specific rules to identify threats. While CrowdStrike initially relied on this method, they now primarily use AI to detect more complex threats, though rule-based analysis is still part of their system.
AI Analysis: CrowdStrike developed AI systems by tracking the "click patterns" of human analysts when identifying threats. The AI now uses these patterns to autonomously detect future threats, reducing the need for manual intervention and increasing efficiency in threat detection.
Overall, Falcon software operates as a single, customizable agent, offering detailed, adaptable monitoring tailored to each client's cybersecurity needs. The system tracks data from various cloud endpoints, relays it to a graph database, and acts on the information. This agent-based model can be updated and enhanced with specialized "modules" to address specific threats, providing clients with tailored solutions that adapt to their unique security challenges [19].
A graphic to explain this five-step process is provided below.
Financials & Unit Economics
CrowdStrike has displayed a strong financial growth profile since going public. This growth can be attributed to the firm’s dominant market position, and disruptive product profile [12].
Additionally, Crowdstike displays many other key performance indicators in its last annual report (2024) that display a strong growth profile [12].

Net Retention Rate (NRR): The company’s NRR was 119%, meaning it retained 119% of revenue from existing customers. This indicates 19% growth in contracted revenue, showing that even without new customers, CrowdStrike could achieve 19% revenue growth.
Crowdstrike’s services typically have specialized pricing that is negotiated between CrowdStrike and the client. However, the firm’s subscription pricing typically follows a standardized format with three pricing packages [13].
Falcon Pro: provides EDR and threat intelligence with Falcon Prevent and X. The overall charge is $7 per endpoint per month.
Falcon Enterprise: prevents and detects attacks beyond malware and stops breaches with complete antivirus visibility. Enterprise adds three new products to the previous package: Falcon Insight, Device Control and OverWatch. The charge is $15 per endpoint per month.
Falcon Premium: provides net level breach protection with real time selection, user monitoring, system health checks and quarterly briefing recommendations. Premium adds Falcon Discover and a premium OverWatch feature to the Enterprise package. The charge is $18 per endpoint per month.
GTM Strategy
Overall, CrowdStrike follows a “land and expand” GTM strategy. First, the company aims to attract a client with high expensive marketing to demonstrate its product strength. Then, CrowdStrike locks in the client for a long period and cross sell them multiple solutions over time [1][10].
Due to CrowdStrike’s high price points, new customers will typically negotiate with CrowdStrike about the firm’s contract pricing.
While customers don’t see the value add of CrowdStrike initially, the company typically acquires new customers, after they face a breach while using a competing cybersecurity platform.
Compared to most software verticals, pricing is more demand inelastic, as customers are willing to pay higher prices for high quality security products – which especially pertains to CrowdStrike.
This inelastic demand for CrowdStrike’s solutions provide them a strong return, with CrowdStrike returning $5.51 in ARR for every $1 that they spend on sales and marketing.
Additionally, CrowdStrike provides various other direct and indirect marketing channels to reach customers [1][13].
Indicators of Attack (IoC): For a low fee, CrowdStrike offers IoC services that identify potential attack areas. Clients who initially ignore these warnings often face breaches and later opt for CrowdStrike's solutions to prevent future attacks.
Intelligence Team: CrowdStrike goes beyond many cybersecurity companies by providing clients with specific information about cyber attackers, including names and addresses. This transparency and detailed insight, especially after an attack, fosters long-term customer loyalty.
Inorganic Growth: Although acquisitions are not CrowdStrike's primary strategy, the company has acquired smaller cybersecurity firms, creating opportunities to cross-sell products. Clients are willing to pay more for CrowdStrike's full product suite due to the enhanced integration and viability of its solutions.
Industry Overview
The global cybersecurity market is valued at $193bn, and is growing at a 14% CAGR to 2032, and within that market EDR has a market size of $18.5bn, and a CAGR of 20%. Thus, EDR is currently only 9% of the cybersecurity market, and growing at 1.5x the CAGR of the overall market [14][15].
Using CrowdStrike’s current revenue figure of $3.4bn and its 36% YoY growth, the company has an 18% market share of EDR, and is rapidly acquiring market share, as its growth rate is faster than the overall sector.
The main reason for CrowdStrike’s rapid growth of market share is due to the disruptive nature of its products, allowing the company to outperform competitors. The competitors can be split into four groups: (1) legacy competitors, (2) next-generation cybersecurity companies, (3) Microsoft (which deserves its own category due to the nature of its “product”), and (4) Fringe cybersecurity providers [1].
An outline of the legacy competitors is provided below. These are larger companies that have a more on-premise data architecture, rather than using the cloud. The weak AI enablement, and manual processes of these companies, makes them less capital efficient and lower margin businesses than CrowdStrike [1].
Symantec: Is one of the oldest legacy providers that focuses on selling on-premise perpetual cybersecurity licenses and they only launched their cloud endpoint technology in October of 2019.
Trend Micro: is also a legacy provider that launched its endpoint security solution in 2019, and labeled it as “Apex One”. Trend Micro mostly focuses on semiconductor technology, with its cybersecurity software used more for its semiconductor business.
McAfee: Is akin to Symantec as one of the first cybersecurity providers, and George Kurtz’s old firm. The business launched its cloud software earlier than other legacy competitors in 2018, but to date the company only serves 50% of its clients through the cloud. In 2021, McAfee also sold its B2B security business to a private equity firm, meaning today it mainly serves consumers.
Additionally, there are many next-generation cybersecurity businesses that incorporate AI and the cloud. These are the main competitors that threaten CrowdStrike’s market presence [1][13].
VMWare: which mainly provides cybersecurity through its subsidiary Carbon Black that it acquired for $2.1bn in 2019. Carbon Black doesn’t have managed threat hunting as a manual service, meaning they lack the human-in-the-loop defense layer of Crowdstrike.
Cylance: provides many similar EDR solutions to CrowdStrike, however, it has worse relationships with cloud providers. Consequently, Cylance has worse integration than Crowdstrike and many other cybersecurity providers.
Sentinel One: is a significant competitor to Crowdstrike, with twice as many customers, but only 25% of the average customer value (ACV) of CrowdStrike. While they service 37 Fortune-500 businesses, their low ACV means that they mainly service small to medium sized businesses that are less retentive, and more likely to churn.
Zscaler: provides system based cybersecurity solutions as a “cloud firewall”, rather than CrowdStrike’s endpoint based security. Zscaler has more use cases than CrowdStrike as its firewall can protect many web-based applications, however CrowdStrike performs better in its EDR niche.
One of Crowdstrike’s key competitors is Microsoft, as the company has quickly penetrated the cybersecurity space [1].
Microsoft sells its security solutions through enterprise license agreements (ELAs), which allow independent companies to sell their products through windows.
Thus, Microsoft doesn’t need to directly sell its own cybersecurity products, but it can charge third-party providers a fee to sell their system into the Microsoft ecosystem.
As will be explained below, CrowdStrike must also go through this process to sell its solution through Windows, and it’s one of the key reasons that led to the CrowdStrike outage in July.
However, as CrowdStrike is dominant in the security industry, it may allow them to exert pressure on Microsoft to lower prices to continue using their system, or to establish future contracts that allow CrowdStrike to sell to clients without paying Microsoft.
Finally, there are various fringe competitors in the cybersecurity space that are worth addressing. Many of these companies are nascent, and don’t have the scale or AI technology of CrowdStrike. With greater funding, there is a threat that they could become tenable competitors, however, today they are still small players [1].
FireEye: provides similar EDR solutions to CrowdStrike, while also providing network and email security. FireEye is not completely cloud based, and its network/email solutions are more commiditized as that market is very saturated.
Tenable.io: mainly focuses on vulnerability management for operational technology platforms that monitor/manage industrial processes such as manufacturing or mining. While Tenable.io specializes its sales for this specific sector, Crowdstrike provides more general cybersecurity which is more applicable to more clients.
Rapid7: provides a wide range of vulnerability management solutions, with open source capabilities as well. Rapid system’s products such as InsightVM, Insight IDR, and Metasploit have more widespread use-cases due to their open source nature. However, it also means the business is less profitable and still doesn’t perform better than Crowdstrike in EDR.
Palo Alto Networks: is known for acquiring smaller cybersecurity providers and then integrating them into their overall platform. While this strategy allows for fast initial growth, Palo Alto has faced integration issues with acquired companies. Thus, the company it faces slower long term growth and lower product quality than CrowdStrike.
Section 3: The Outage
Overview on the Outage
On July 19, 2024, Microsoft Windows systems around the world had an outage where they all got stuck on a blue screen with a message that displayed “critical failure”. Later during the day CrowdStrike confirmed that there was an update for their Falcon software that malfunctioned and caused all the Windows computers it was installed in to crash. The outage led to many issues, with 512 US flights being canceled, stock exchanges freezing, 911 emergency lines malfunctioning, and 8.5mm computers crashing [16].
However, a solution to the issue was quickly found, as Microsoft recommended that clients reboot their computers into “Safe Mode”, and then delete the faulty Falcon file “C-00000291.sys.”
The outage was a shock to most, as it was unbelievable that one update failure could have an impact on so many computer systems. While typically malfunctions have a smaller impact, there were several catalysts during this update that led to a widespread outage.
What Caused the Outage?
The structure of typical software systems is bifurcated into a “kernel” layer and a “user” application [17].
“Kernel code” represents the overall software network that communicates with hardware, devices, memory, and storage within the system [17].
The kernel can see the whole system landscape at any moment, and the reason kernel code crashes is to prevent malicious code from causing further damage to files.
The malware doesn’t have a chance to continue infecting a software if the whole system shuts down.
An interesting fact is that the shut down screen was blue because that is Windows's crash configuration. If the crash happened on Linux or MacOS the screen would be black or pink respectively.
User applications are individual platforms within the kernel code where applications can run [17].
The kernel code provides top level information that the user application then employs within its “user map”. The limit on the information that the kernel provides is also known as the “kernel boundary”.
If the user application wants to go outside the kernel boundary it must send a request to the kernel code, that the kernel must then see and accept.
When the user application crashes only the application crashes, while if the kernel crashes, the whole system (including the user apps) crashes.
Crowdstrike's Falcon software operates at the kernel level, analyzing application behavior to identify potential attacks, rather than relying on file labels at the application layer. This kernel-based approach necessitates device-specific coding, even though Falcon is designed for endpoint application-level security, not hardware targeting [17].
Microsoft understands that it’s risky for third-party providers to access the Windows kernel code, so they mandate that these providers receive certification first. The certification for Windows’ kernel code is called Windows Hardware Quality Labs (WHQL), which certifies that a software has been checked by the vendor and has passed Windows’ quality labs testing to access the kernel operating system [17].
CrowdStrike initially passed the WHQL certification, however, as they were looking to release their newest update they didn’t want to go through the whole WHQL process again, as it has a very slow turnaround time [17].
Thus, Crowdstrike opted to update its system through a definition file, which simply changes the instruction at the operating layer of the initially certified software.
Windows couldn’t see that the software had changed, and the solution was good-to-go, as it already had WHQL certification.
The Falcon system with the new driver then remotely installed the new Falcon update into the Windows kernel code.
Then, while the code was updating there seemed to be a key flaw in the program which allowed any malware to enter and disrupt the system for a brief period of time. It’s assumed that a small bug then entered the system, and forced the enter Windows kernel code to crash, as the kernel hoped to protect the entire operating system from the breached malware.
Post-Mortem Analysis
After the outage, there were several key findings by government entities and independent search parties, as they manually dissected the outage to find its causes [17].
It seems that within the definition driver there was an attempt to move code from one registry to another (registry 8 was moved to 9), when it shouldn’t have been switched.
The data file for the update was also downloaded as a “.sis” file when it should have been a different format.
There also seems to be inadequate parameter valuation systems in Windows, as the system should have shut down the function if the code failed, not shut down the kernel code.
Finally, the reason this update got past Windows’ post-WHQL security is because it was installed as a “boot driver”. A boot driver is a driver that needs to be installed to even start the Windows operating system.
Thus, Windows needed this update to even start its post-WHQL security systems that are then supposed to check the kernel code for a potential malfunction.
As cybersecurity systems outpace traditional security systems, there are various risk and mitigation efforts that should be taken by security companies [18].
Automatic Updates: should be closely monitored with multiple checks and balances, and should very rarely enter the kernel-code layer. If they do enter the kernel-code there should be multiple manual checks and balances to ensure that the software is being safely updated.
Canary Developments: updates should first be executed in controlled environments before they enter the actual kernel code.
Decentralized Updates: rather than having the entire system on one centralized command chain that can be disrupted by malfunctions, companies should invest in decentralized systems that don’t rely on a central point of update, as that could make the whole system susceptible to a crash.
Section 4: Future Outlook
Opportunities
CrowdStrike has various opportunities in EDR and the overall cybersecurity space that can allow it to rapidly increase its potential returns. AI presents the largest opportunity by far, as it prevents many future advantages for CrowdStrike [6].
Replacement & Integration: Falcon's AI advancements have replaced open-source vendors, Microsoft consoles, and next-gen vendors, and its adaptability ensures seamless integration with diverse platforms to meet evolving client needs.
Efficiency: By leveraging AI-enablement, CrowdStrike aims to enhance its efficiency, monitoring capabilities, and vulnerability management. Notably, AI integration has already yielded a 50% reduction in manual agents on the Falcon system within a year, paving the way for continued AI adoption to drive further margin expansion and scalability.
Analysis & Reuse: CrowdStrike collects data once and reuse it many times. AI makes cybersecurity more predictive and accessible for all skill levels, increasing the business’s overall customer satisfaction.
Additionally, there are various other opportunities that can allow for future market penetration, and overall expansion [6].
Identity Protection: refers to security solutions that protect the identity data of clients. Typically, the vast majority of attacks target identity data, (80% of attacks) as it provides access to sensitive financial information. Crowdstrike has recently entered this space and has already approached $300mm in ARR. Through enabling its AI in this sector CrowdStrike could outpace legacy competitors and penetrate a new market.
Cloud Security: in the last year CrowdStrike has tracked a 75% increase YoY in cloud security based attacks due to the decentralized nature of the cloud. As more clients use cloud-based technology to house their software, it presents an opportunity to expand its solutions outside of EDR to the overall cloud.
Challenges
However, along with its opportunities, CrowdStrike must surpass various potential challenges that could threaten its future business [6].
Customer Trust: Trust is a pivotal tenet of the cybersecurity space, and one of the reasons that CrowdStrike expanded so quickly is because they provided security for clients, when competitors failed. With the recent outage, clients have become unhappy with CrowdStrike, and it may decrease the firm’s future revenue growth.
Commoditization: With various new entrants into the cybersecurity space, and many next generational security companies providing EDR solutions, CrowdStrike’s software may be akin to a commodity with little differentiation. Currently, the catalyst of AI may quell these fears, however, it presents a potential risk to the company in the long term.
Supplier Pressure: As explained above, Microsoft charges a rate for CrowdStrike to sell its products on the Windows software. With the recent outage and Microsoft’s increase in scale, CrowdStrike may be charged even higher prices to run its solutions, contracting its future margins.
Lessons Learned
The story of CrowdStrike, provides insight for business executives and investors that are interested in technology, and more specifically the cybersecurity space.
CrowdStrike is a great example of a company that did the hard work first. Specifically, CrowdStrike gained intelligence through its manual services and focused on research and development very early in its lifecycle, providing it with a strong foundation for growth.
Additionally, CrowdStrike presents a framework for how a business should be grown from its initial foundation. The company pursued a disciplined growth strategy through financing, customer acquisition, and expanding its product suite.
Finally, while most software companies have a heavy focus on GTM, CrowdStrike shows how putting the product first is essential in some industries, namely cybersecurity. As a first mover in AI, incident response, EDR, and the cloud, CrowdStrike made its software an invaluable asset to customers.
First, CrowdStrike’s story is one of creating a solid foundation. George Kurtz and the initial Crowdstrike team built a strong base to bolster the business’s future growth.
CrowdStrike’s initial manual services business model was unattractive to inventors at the time. However, it created trust with clients and expanded the firm’s overall intelligence in cybersecurity that it was later able to implement into its software system.
When CrowdStrike started, endpoint protection and cloud-based cybersecurity were new concepts. Instead of waiting for the technology, CrowdStrike built preliminary cloud infrastructure, gaining a first-mover advantage in EDR and cloud security over legacy vendors.
These lessons are especially important in today’s software environment as many start-ups claim to use their own proprietary AI systems, when in reality they might be implementing “ChatGPT wrappers”.
Since investors may lack the technical expertise to validate software, CrowdStrike shows that they can instead qualitatively assess a founder's ability to build a strong foundation before pursuing growth.
Next, CrowdStrike provides a great example of strategic decision making to scale a company's solutions. As the software space is notoriously competitive, this growth stage is essential for the survival of most companies, and CrowdStrike provides a framework of how to pursue it.
Since its inception, CrowdStrike has focused on a product based expansion strategy. As cybersecurity has a stronger focus on product viability than sales, Kurtz focused on emboldening key solutions such as AI, EDR, the cloud, and threat intelligence before competitors.
However, this growth required financing, and while most start-ups would avoid losing ownership in their business for funding, CrowdStrike was willing to take the sacrifice to bolster future growth. In each financing round CrowdStrike raised record amounts of funding, while still retaining control of the business.
Finally, CrowdStrike also employed a differentiated GTM strategy, which focused on acquiring customers through trust rather than generic sales calls. The firm’s incident response teams solved security issues for clients when competitors had failed, providing clear rationale for why they should switch to CrowdStrike.
With the exponential pace of new software start-ups it can be difficult for investors to understand technical jargon and which companies are the real-deal. However, CrowdStrike provides a framework for how investors can apply traditional financial concepts to this rapidly expanding sector in three key steps.
Analyzing the foundation of a business to see if it can sustain growth
Validating its core go-to-market strategy
Understanding how it will continue to stay differentiated in its sector
Sources: [1], [2], [3], [4], [5], [6], [7], [8], [9], [10], [11], [12], [13], [14], [15], [16], [17], [18], [19]
Interested in our updated reading / wellness list? Check it out here.
Got Feedback? Just hit Reply. Seriously, I would love to get your thoughts.
Interested in our IB / PE / Finance course recommendation? Check it out here.
Looking for more Pari Passu Content? Check out Instagram | Twitter | Linkedln